Report on the Cyber Security Alerts Received by CERT-RO During 2013
Author(s): CERT, RO
Issue: Volume 3, Issue 1, Year 2014
1. Summary of the report
The Romanian National Computer Security Incident Response Team – CERT‑RO is an independent structure, with expertise in the field of cyber security that has the capacity to prevent, analyze, identify and respond to cyber security incidents threatening our national cyber-space. CERT-RO is coordinated by the Ministry for Information Society and is fully financed by the state budget.
As a national contact point in the matter of cyber security incidents, during 2013 (1st of January – 31st of December), CERT-RO was informed by various domestic or international partners, about several cyber security incidents that affected our national cyber-space, as follows:
- Alerts collected and transmitted by automated systems: 43.231.149.
- Total number of compromised unique IP’s extracted from the alerts: 2.213.426.
- Individual alerts, manually collected, and alerts created on the basis of data collected by CERT-RO: 450.
The objective of this report is to analyze the cyber security alerts collected / managed by CERT-RO in 2013, in order to obtain an overall view of the nature and dynamics of this types of events relevant to the evaluation of the risks targeting the IT&C systems in Romania.
Based on the collected data, the following have been observed:
- Over 16% of the total number of IPs allocated to Romania (approx. 13.5 million) were involved in at least one cyber-security alert reported to CERT‑RO in 2013;
- Approximately 78% of the alerts refer to systems in Romania that have been compromised through the exploitation of some technical vulnerabilities and got infected with different versions of malware and have become part of a botnet; the total number of unique IPs identified is 1,945,597, and represents 14% of the total IPs allocated to Romania.
- Over 16% of the alerts refer to systems in Romania, compromised by attackers that have exploited some misconfigurations on DNS servers, and used the servers for launching further attacks on other targets in Internet (DNS amplification attacks, DNS cache poisoning etc.).
- More than 5% of the alerts refer to entities within Romania that sent spam emails to various targets on Internet;
- 40% of all the alerts refer to systems in Romania infected with the Conficker worm; according to the collected data more than 12,5% of the total number of IPs allocated to Romania have been reported to CERT-RO as being infected with Conficker; the worm, identified in 2008, targets Microsoft Windows systems without the latest security patches installed;
- 50% of all the unique IPs reported to CERT-RO, were identified as running Microsoft Windows operating systems, versions 98, 2000, XP or 2003;
- Over 39% of the individual alerts (5.2) refer to entities in Romania that host phishing web pages, affecting the activity of financial institutions in Romania and abroad;
- 10,239 .ro domains were compromised in 2013, representing approx. 1.4% of the total number of .ro domains; 60% of these domains were infected with various types of malware;
- 61 IPs were reported as infected with various types of APTs.
The above findings lead to the following conclusions:
- Cyber security threats upon our national cyber-space have diversified, and have evolved both in terms of quantity and in terms of technical complexity;
- The majority of the compromised systems in Romania, are part of botnets, being used as proxies for carrying out attacks on targets outside the country, thus representing potential threats to other systems connected to Internet;
- Based on the analysis of the malware types specific to our national cyber-space and of the types of compromised systems, both revealed in this report, it appears that, in quantitative terms, most attacks are directed towards outdated, obsolete systems, lacking security features (e.g. systems affected by Conficker) or are not updated with the latest security patches/updates;
- An increasing number of entities in Romania become targets of APTs, attacks with a high degree of complexity that are launched by groups with the capacity and motivation to persistently attack a target in order to obtain certain benefits (usually sensitive information); it is expected an increase in the number and severity of such attacks nationwide during 2014;
- Romania cannot be considered anymore just a generator of cyber security incidents, because the analysis of the data presented in the current report demonstrates that is mostly used as a proxy by other attackers.
2. About CERT-RO
The Romanian National Computer Security Incident Response Team – CERT-RO is an independent structure, with expertise in the field of cyber security that has the capacity to prevent, analyze, identify and respond to cyber security incidents threatening our national cyber-space. CERT-RO is coordinated by the Ministry for Information Society and is fully financed by the state budget. CERT-RO’s main tasks are:
- organizing and maintaining a national database regarding threats, vulnerabilities and cyber security incidents identified by or reported to CERT‑RO, techniques and technologies used for attacks as well as good practices regarding cyber infrastructures protection;
- provides the required organizational and technical support for information exchange between different CERT teams, users, regulators, equipment and cyber security solutions providers and internet services providers;
- provides a unique contact point for collecting information and complaints about cyber security incidents in an automated and secured manner, or through direct communication, depending on the case;
- elaborates legislative proposals, submitted to the Ministry for the Informational Society (MSINF) or to the Supreme Council for National Defense (CSAT), regarding the changes that apply to the legal framework in order to foster the improvement of cyber security of the systems used to provide services of public interest;
- constitutes the “Early Warning and real-time information System”(EWS), regarding cyber security incidents. Its main goals are: sending real-time alerts on cyber security incident, issuing reports on the distribution and nature of the cyber security incidents and facilitating collaboration with national authorities responsible for cyber security, in order to prevent and eliminate the effects of the cyber security incidents;
- provides public services such as: preventive services (announcements of new threats or vulnerabilities identified at a national or/and international level; security audits, risk assessments and penetration testing on demand; reports regarding cyber security incidents that could affect or involve Romanian entities), reactive services (alerts and warnings regarding suspicious activities possibly preceding an attack, handling of cyber security incidents at national level), and consultancy services (CERT teams training, risk analysis regarding cyber infrastructures applicable to local and national level).
CERT-RO collects data, regarding cyber security incidents and events affecting or involving entities in Romania, from national or international sources. Thus, once an incident is identified, based on the internal procedures, CERT-RO deploys a series of actions that ensure its response activity. In most cases, the main goals of the incident response activity, regarding cyber security incidents, are as follow:
- Immediate stopping or mitigation of the effects of the incident (e.g. shutdown, takedown of the malicious server etc.);
- Preliminary analysis of the impact generated by the incident/event;
- Identification and alerting of all affected parties, or parties that could be affected by the cyber security incidents/events and those responsible for remediation of the situation;
- Identification and alerting of all institutions or public authorities responsible for managing the situation;
- Dissemination of technical documents regarding methods for detection and mitigation of cyber security incidents, useful for other entities that may be affected by a similar incident.
According to its legal attributes, CERT-RO provides the organizational and technical support for information exchange between various entities (national authorities, individuals or companies, CERT teams, security solution providers, internet service providers, etc.) involved in cyber security incidents, and ensures their good cooperation.
CERT-RO does not have legal authority for solving all kinds of cyber security incidents. For example the cyber security incidents that had resulted from cybercrimes are the responsibility of the law enforcement agencies, according to their legal competence. Also, according to the law, cyber security incidents that could constitute threats to the national security are managed by institutions with competence in this specific domain. If CERT-RO receives such notification, it will forward them to the proper authority.
3. The objective of this report
The objective of this report is to analyze cyber security incidents reported to CERT-RO, between 01.01 – 31.12.2013, in order to obtain a general overview of the nature and dynamics of these types of events/incidents, relevant for assessing cyber security risks targeted at the IT&C infrastructures within Romania, that are in CERT-ROs constituency.
Based on the data collected, meaning incidents reported to CERT-RO by various public or private entities and other data collected from the public sources by CERT-RO specialists, this document contains the main categories of incidents that affected the Romanian national cyberspace in 2013.
For a better evaluation of the information presented in this document, it is relevant to mention that CERT-RO has not received all the data regarding cyber security incidents that affected or involved resources of the Romanian national cyberspace. Even so, the volume of the data analyzed is considered sufficient to fully characterize the current state of security of the Romanian cyber infrastructure.
The statistics presented in this report are mainly based on information obtained from different sources, regarding URLs and IP addresses detected as performing suspicious or malicious traffic in the Internet.
We consider necessary to provide some clarification on the common terms used in this report. Thus, in the content of this document we will refer to the following terms:
- Cyber security event – any event or situation relevant in terms of cyber security, that can cause a change of normality within a system and indicate a possible violation of its security policies, or a failure of the protective measures that could be highlighted and properly documented;
- Cyber security incident – an event within the cyber space that has consequences or affects cyber security of a system, or any action, contrary to any regulations enforced, regarding computer systems, which may consequently affect or already affected its cyber security, or may lead to compromising the information processed by it.
- Cyber security alert – any cyber security incident or event reported, that involves or may involve entities from Romania.
4. CERT-RO’s data sources
CERT-RO collects data regarding cyber security incidents, events or alerts from several sources, as follow:
- Alerts collected and transmitted via automated systems (eg: honeypots). Those types of alerts are sent only by specialized organizations, such as CERT’s or other security companies, which have in their possession cyber security incident detection systems. The number of these kinds of alerts is significantly higher than other types and can reach values around 500,000 daily alerts.
- Individual alerts, reported by various entities – individuals or legal persons from Romania and abroad. The number of this kind of alerts reaches 5-10 daily;
- Information collected by CERT-RO, from various sources. These sources includes various information collected from public or restricted sources, such as specialized websites or security companies, about specific vulnerabilities, cyber security threats or incidents.
The nature of the reported alerts, as well as the quantity of available data for each of the categories requires a different approach for each case.
Alerts sent by automated systems require automatic processing. In this case, the received data it resumes to lists of IPs detected as doing malicious or suspicious activities over the Internet, and some extra details about the suspicious activity (timestamp, incident type, used ports, the attack etc.). Most of these alerts are automatically processed by CERT-RO and are sent to the ISPs who own the networks that contain the system which triggered the alert. Most of the time, in this type of alerts, CERT-RO has no exact information about the real user behind the IP address, so the identification process is passed to the internet service provider (ISP). Also, the ISP has the responsibility to forward the alert to the real client. Although this type of alerts does not provide details about the target, they provide an overview of the types of cyber threats that are affecting Romanian cyber infrastructures.
Individual alerts as well as the alerts collected by CERT- RO, are considerably reduced in number, but the reported information about the incident is much more accurate and relevant (the affected organization, the source of the attack and the vector of attack). In most of the cases, the data is collected by CERT-ROs analysts from the affected entities, along with incident reporting. Statistically speaking, these types of alerts are valuable, because they reflect better the state of national cyber security.
5. The Early Warning System (EWS) of CERT-RO
CERT-RO operates a pilot project for an Early Warning and Real-Time Information System (EWS), that is designed as a collection of procedures and systems that processes all received alerts, in real time, in order to immediately warn affected parties (ISP , individuals or legal persons directly affected , etc.), as well as for publishing reports regarding the distribution and nature of cyber security incidents and for collaborating with national authorities with responsibilities in cyber security and cybercrime fields, in order to prevent and eliminate the effects of the incidents. This report is based on the alerts processed during 2013 by the EWS of CERT- RO.
6. Statistics based on the alerts received
6.1. Alerts collected and transmitted through automated systems
In the reference period (01.01 – 31.12.2013), CERT-RO received the following alerts:
- Total number of automatic alerts received: 43.231.149
- Total number of unique IP extracted from all alerts: 2.213.426
Depending on the content of each alert, the alerts were sorted into various classes and types of alerts according to Table 1.
6.1.1. Distribution of alerts based on types and classes
The table and the graphic below show the distribution of the alerts received based on classes and types of alerts. Some of the unique IPs reported can be found in several types of alerts.
| Alert Class | Alert Type | Alert number |
| Botnet | Botnet Drone | 33.677.871 |
| Vulnerabilities | Open Resolver | 6.782.888 |
| Abusive Content | Spam | 1.986.605 |
| Information Gathering | Scanner | 603.524 |
| Malware | Malicious URL | 116.535 |
| Cyber Attacks | Bruteforce | 30.150 |
| Vulnerabilities | Open Proxy | 13.809 |
| Fraud | Phishing | 13.556 |
| Botnet | Botnet C&C Server | 4.082 |
| Malware | Infected IP | 1.840 |
| APT | RedOctober | 287 |
| Compromised Resources | Compromised Router | 2 |
| TOTAL | 43.231.149 | |
The alerts from “Botnet Drones” category (computers infected with various malware, which are part of different botnet networks) predominates with a 78% percentage of the total alerts received in 2013. The total number of identified unique IPs based on the reported alerts is 1,945,597, which is 14% of the total number of IPs allocated to Romania.
6.1.2. Monthly distribution of alerts
The graph below represents the distribution of alerts per month, meaning the month in which they were received by CERT-RO.
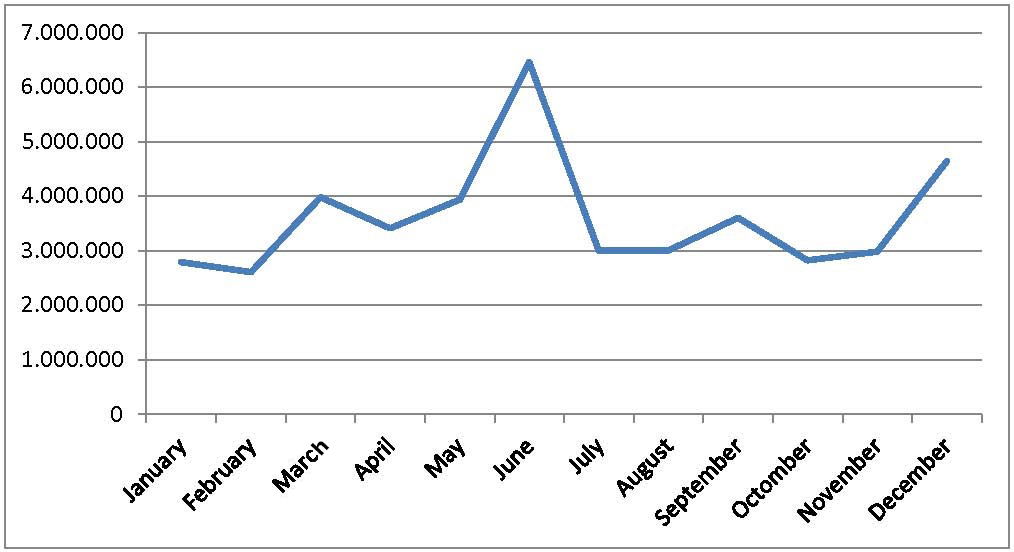
Fig. 2. Distribution of alerts per month
6.1.3 Distribution of alerts by Autonomous System Number (ASN)
Furthermore, the received alerts were distributed by ASN’s (Autonomous System Number, http://en.wikipedia.org/wiki/Autonomous_System_Number), according to the IP address of each alert. The received alerts have targeted 1148 unique ASNs from Romania, this number covering almost all Romanian ASNs (http://bgp.he.net/ country/RO). The table and chart below represents the top 30 internet service providers (ISP), who own IPs that were detected as generating malicious traffic, visible on the internet (sorted by the number of hosted compromised IPs). Usually, an ISP has assigned one or more ASN’s.
| No, | AS NUMBER | AS NAME | Percent (%) |
| 1 | 8708 | RCS & RDS SA | 35,96 |
| 2 | 9050 | Romtelecom | 32,27 |
| 3 | 6830 | UPC | 7,88 |
| 4 | 6910 | Dial Telecom S.R.L | 3,46 |
| 5 | 48161 | SC NextGen Communications SRL | 2,68 |
| 6 | 12632 | RCS & RDS SA | 2,27 |
| 7 | 12302 | Vodafone Romania S.A. | 1,36 |
| 8 | 8953 | Orange Romania SA | 1,17 |
| 9 | 2614 | RoEduNet | 0,45 |
| 10 | 35725 | COSMOTE Romanian Mobile Telecommunication SA | 0,33 |
| 11 | 34711 | DIGINET SA | 0,31 |
| 12 | 41496 | TV SAT 2002 SRL | 0,29 |
| 13 | 39743 | Voxility S.R.L. | 0,25 |
| 14 | 6663 | Euroweb Romania SA | 0,24 |
| 15 | 39737 | Net Vision Telecom SRL | 0,24 |
| 16 | 44563 | ENIASAN SRL | 0,24 |
| 17 | 15471 | S.N. Radiocomunicatii S.A. | 0,22 |
| 18 | 50604 | SC MEDIA SUD SRL | 0,22 |
| 19 | 41273 | Electrosim SRL | 0,22 |
| 20 | 47148 | STARNETRANS SRL | 0,22 |
| 21 | 41571 | Transilvania Digital Network SA | 0,21 |
| 22 | 35002 | SC NextGen Communications SRL | 0,20 |
| 23 | 51102 | IMPATT SRL | 0,20 |
| 24 | 39543 | TENNET TELECOM SRL | 0,18 |
| 25 | 31605 | Canal S SRL | 0,18 |
| 26 | 40997 | TITA & Company SRL | 0,17 |
| 27 | 35664 | CCC Blue Telecom SA | 0,17 |
| 28 | 31102 | TV Adler-Trading SRL | 0,17 |
| 29 | 39464 | Star Design I&E SRL | 0,15 |
| 30 | 44605 | TeleCablu&Net Srl | 0,15 |
| Others | 7,96 |

Fig. 3. Top 20 ASNs that host malicious IPs
Note:
The presence of a compromised/infected IP in an ISP’s network does not mean that the Internet service provider (ISP) is guilty for that incident. Most times, the infected IP that generated the alert is a customer of that ISP, thus the responsibility for the generated traffic (according to art. 13 of Law 365/2002 and other regulations in the field), disinfection and proper system security goes to the client in discussion.
6.1.4. Types of malware frequently present into Romanian cyberspace
In about 75% of the received alerts, it was possible to identify the malware type which affected the compromised system. In this regard, it was issued a “Top 25” of the most common types of malware from the Romanian cyberspace.
| # | Malware type | Percent (%) |
| 1 | Conficker | 53,4543 |
| 2 | Sality | 10,9534 |
| 3 | Citadel | 8,2338 |
| 4 | Pushdo | 6,7392 |
| 5 | Zeroaccess | 3,1662 |
| 6 | Slenfbot.5050 | 3,0855 |
| 7 | Virut | 1,5755 |
| 8 | Kelihos | 1,3314 |
| 9 | IRCBot | 0,9238 |
| 10 | Zeus | 0,5706 |
| 11 | Trafficconverter | 0,3484 |
| 12 | Grum | 0,1508 |
| 13 | Torpig | 0,0252 |
| 14 | Ransomware | 0,0199 |
| 15 | Blackenergy | 0,0127 |
| 16 | Tdss | 0,0075 |
| 17 | Trojan.Iframe.BMY | 0,0045 |
| 18 | Neurevt | 0,0038 |
| 19 | Trojan.Script.CEV | 0,0031 |
| 20 | Hermes | 0,0025 |
| 21 | Dorkbot | 0,0024 |
| 22 | DDoS_Khan | 0,0023 |
| 23 | DDoS_DirtJumper | 0,0022 |
| 24 | Gamarue | 0,0017 |
| 25 | Trojan.Iframe.BZW | 0,0016 |
According to Wikipedia.org, “Conficker”, also known as “Downup”, “Downadup” and “Kido”, is a computer worm targeting the Microsoft Windows operating system that was first detected in November 2008. It uses flaws in Windows software and dictionary attacks on administrator passwords to propagate while forming a botnet, and has been unusually difficult to counter because of its combined use of many advanced malware techniques. Conficker’s final goal is to obtain control over infected computer, which can then be controlled remotely. According to the analyzed data, 1,693,323 unique IPs (76% of all reported IPs or 12.5% of all unique IPs from Romania) are infected with this worm.

Fig. 4. Top 25 malware types in Romania in 2013
6.1.5. Types of operating systems affected by alerts
In about 11% of the received alerts it was possible to exactly identify the type of operating system of the affected client. Therefore, the table below shows a ranking of the most affected types of operating systems installed onto Romanian systems.
| # | Operating system | Total no. of alerts |
| 1 | Windows | 4.344.677 |
| 2 | Solaris | 55.524 |
| 3 | Linux | 8.532 |
| 4 | ChacheFlow | 698 |
| 5 | FreeBSD | 95 |
| 6 | OpenBSD | 69 |
| 7 | NetBSD | 61 |
| 8 | Novell | 25 |
| 9 | Cisco | 23 |
| 10 | Checkpoint | 9 |
| TOTAL | 4.409.713 | |
According to data reported to CERT-RO, most infected Windows operating systems run the 98/XP/2000/2003 versions. Some of these versions are no longer supported by the manufacturer, them already being declared as “end of life” versions, and other versions will not receive support in the near future. These versions of Windows operating systems run on approx. 50% of all unique IPs reported to CERT-RO.
6.2. Individual alerts
Along with automated alerts, CERT-RO analysts received a series of cyber security incidents reported directly by individuals or organizations located in Romania and abroad, such as:
| Alert Class | Alert Type | Alert no. |
| Fraud | Phishing | 173 |
| Malware | Infected IP | 95 |
| Information Gathering | Scanner | 43 |
| Cyber Attacks | DDoS | 42 |
| Malware | Malicious URL | 31 |
| Abusive Content | Spam | 11 |
| Botnet | Botnet Drone | 11 |
| Compromised Resources | Compromised Website | 7 |
| Cyber Attacks | Exploit Attempt | 7 |
| Compromised Resources | Defacement | 6 |
| Compromised Resources | Compromised Network/System | 4 |
| Abusive Content | Disclosure of Confidential Data | 3 |
| Fraud | Unlawful eCommerce/Services | 3 |
| Other | Other | 3 |
| Abusive Content | Disclosure of Personal Data | 2 |
| Botnet | Botnet C&C Server | 2 |
| Compromised Resources | Comprimised Application/Service | 2 |
| Cyber Attacks | APT | 2 |
| Abusive Content | Child Pornography | 1 |
| Cyber Attacks | Bruteforce | 1 |
| Information Gathering | Social Engineering | 1 |
| TOTAL | 450 | |

Fig. 5. The distribution of individual alerts
Depending on the affected entity type, the incidents distribution is the one presented in the chart below. It is worth mentioning that the affected entities are not necessarily individuals or legal persons from Romania.
| # |
The type of affected entity |
No. of alerts |
| 1 | Banking institutions | 142 |
| 2 | Private institutions | 80 |
| 3 | Education institutions | 29 |
| 4 | Public institutions | 18 |
| 5 | Natural persons | 17 |
| 6 | ISP | 5 |
| 7 | ”Law enforcement” agencies | 1 |
| 8 | Not specified | 158 |
| TOTAL | 450 | |
Also, depending on the affected system type, the distribution of security incidents is as follows:
| # | Type of affected system | No. of alerts |
| 1 | Networks | 180 |
| 2 | Banking/payment services | 132 |
| 3 | Web sites | 85 |
| 4 | 18 | |
| 5 | Workstations | 15 |
| 6 | Social Networks | 3 |
| 7 | Databases | 2 |
| 8 | Not specified | 15 |
| TOTAL | 450 | |
6.3. Statistics on “.ro” compromised domains
The received alerts often refer to “.ro” domains affected by various types of incidents. Thus, for the reference period, CERT-RO holds data of 10.239 compromised domains.
From a total number of 710.000 domains registered in Romania (according to ICI ROTLD data), in December 2013, the number of “.ro” domains reported to CERT RO as being infected represents a percentage of about 1.4%.
The distribution of affected domains, by incident types, is found in the table below.
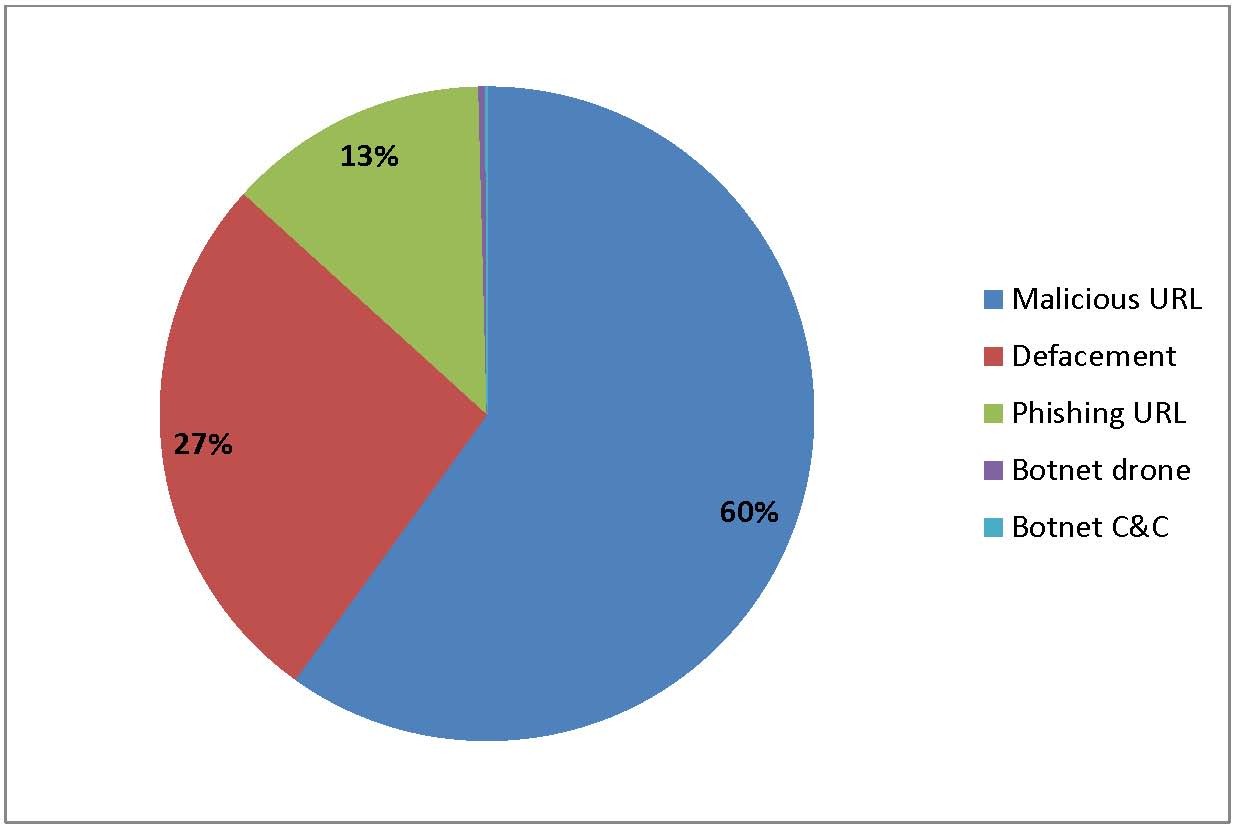
Fig. 6. Compromised “.ro” domains

Fig. 7. Compromised .ro domains – alerts distributed by month
6.4 Advanced Persistent Threats (APT)
On February 25th, 2013, CERT-RO received a notification regarding a new cyber threat called “MiniDuke”, which was categorized as a high risk APT, specialized in extracting data from the infected systems, focusing on the entities within the “governmental structures and research institutions” field of activity. The malware associated with the threat was exploiting vulnerabilities in Adobe Reader, was spreading via email using special techniques of social engineering, and was copying files that were subsequently transmitted to the attacker. In Romania, 6 victims were found infected, and for the fulfilling the incident response activities a collaboration with other national authorities with legal competences in Romania was necessary.
Also, during 2013 we received 287 alerts regarding the “Red October” threat. These alerts have targeted 55 unique IPs in Romania, subsequently notified by CERT RO. These kinds of attacks have also been identified during the past year and have targeted government structures or embassies in Romania.
7. Conclusions and comments
By analyzing the data received by CERT- RO and presented in this report, we can conclude that cyber threats targeting the Romanian national cyberspace have diversified, evolutionary trends being observed, both in terms of quantity and of technical degree of complexity.
Most alerts analyzed by CERT- RO, from the automatic or individual segment of alerts, refer to entities in Romania, victims of attacks/attackers that have usually exploited technical vulnerabilities. The main goal of the attacks was to infect the computer systems with various malicious applications in order to make them part of different types of botnets (zombies).
These compromised systems (victims), who pose as real threats to other entities connected to the Internet, are often used to serve as “proxies” for carrying out other attacks on targets outside Romania. There are significant advantages for the attacker for using such an approach, for example the possibility to hide his real identity and also to use of a large number of computers (depending on the number of infected computer systems) to launch attacks.
Also, based on the malware types specific to the Romanian national cyberspace and on the types of compromised systems, it appears that, from a quantitative point of view, most attacks are directed towards obsolete systems, outdated, with no native security features (i.e. systems affected by Conficker) or that are not updated with the latest security patches/updates.
It is worth noting that Romanian entities are becoming more frequent targets for APT threats, respectively cyber-attacks with a high degree of complexity, launched by groups that have the capacity and motivation to persistently attack a target in order to obtain certain benefits (usually sensitive information). Also, given the complexity of some functions possessed by the APT malware (capable of intercepting electronic communications, unauthorized access to data related to financial transactions and electronic means of payment, etc. cyber espionage. ex: Red October, Miniduke), present in a smaller number of alerts within the analyzed period, and that these types of threats show a moderate evolutionary trend, it may be expected a nationwide growth in the number and severity of such attacks, during 2014;
In this context, we maintain our conclusion of the previous report published by CERT-RO for the first six months of the past year, that Romania cannot be considered just a source of cyber-security incidents or threats, but the analysis of the presented data demonstrating the intermediate/transit character of some significant systems connected to the Internet in Romania, used as proxy for launching attacks on other targets in Internet.
Among the main difficulties encountered in the incident response activity, we can mention the lack of explicit legal regulations regarding the responsibilities for notification, responding, prevention and mitigation of cyber security incidents by the state institutions or companies in the private sector, this hindering our activities and the real-time response to such incidents. In this context, we consider necessary to supplement the national legislation framework with the stipulations contained in certain documents that are found at European level.
Title: Report on the Cyber Security Alerts Received by CERT-RO During 2013
Author(s): CERT, RO
Publication: International Journal of Information Security and Cybercrime
ISSN: 2285-9225, e-ISSN: 2286-0096
Issue: Volume 3, Issue 1, Year 2014
Section: Cyber-Attacks Evolution and Cybercrime Trends
Page Range: 65-80
Copyright ©2012-2026
The International Journal of Information Security and Cybercrime (IJISC)
All rights reserved
The International Journal of Information Security and Cybercrime is a trademark of the Romanian Association for Information Security Assurance (RAISA).
No part of this publication may be reproduced, stored in a retrieval system, photocopied, recorded or archived, without the written permission from RAISA. When authors submit their papers for publication, they agree that the copyright for their article be transferred to the Romanian Association for Information Security Assurance, if the articles are accepted for publication. The copyright covers the exclusive rights to reproduce and distribute the article, including reprints and translations.







 ---
--- 